AROBS Transilvania – custom software development company
Cybersecurity Consulting Services
- Home
- Cybersecurity Consulting Services
// Arobs Transilvania Software
Enterprise Cybersecurity Solutions and Information Security for Strategic Development Across Industries
The privilege of increased online accessibility for businesses has come with the price of complex cyber-attacks and threats. These can infiltrate any company’s vulnerable security systems and cause an unexpected loss of financial resources and time. To avoid data and economic loss, enterprise cybersecurity consulting services & penetration testing services come in handy for organizations of all sizes.
Implementing a solid layer of cybersecurity systems and information security for many organizations while maintaining full functionality can be a time-consuming challenge. Our team works with industry–leading technologies that smoothly integrate into your business and implement high-end enterprise cybersecurity solutions in the most convenient timeframe possible for your organization—assuring a continuous activity flow and data safety at the same time.
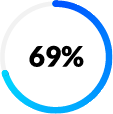
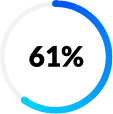
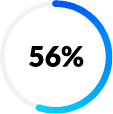
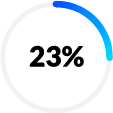
Partnering with a team specialized in cybersecurity services is crucial, as cyber threats are continuously growing. The EC-Council CEH Threat Report 2024 offers a broad perspective on current cybersecurity concerns. During the one-year period covered by the study, companies encountered diverse types of threats.
What Are the Most Common Cyber Threats?
Phishing
Social
Engineering
Security
Misconfigurations
Malware and
Ransomware
Malicious
Insiders
Who We Serve
- Financial & Insurance Companies
- Healthcare Providers
- Manufacturing & Industrial
- Transport & Logistics
- Government & Public Sector
Top-notch team
Our experts are industry-certified and provide high-standard strategies created for future-ready companies that thrive empowered by technology. The AROBS experts conduct vulnerability assessments and evaluate defense capabilities to ensure security standard compliance and incident response readiness through diverse techniques, including a simulation of a potential cyberattack.
Innovation





We Quantify How Risks Translate to Actual Business Impact
| Threat | Risk | Potential Damage |
| Phishing email to executives | Unauthorized access, financial fraud | Wire transfer loss, reputational harm |
| Ransomware | Data encryption, system downtime | Business interruption, extortion payment |
| Cloud misconfiguration | Unsecured sensitive data | Regulatory fines, data breache |
| Vendor system compromise | Supply chain exposure | Service disruption, legal liability |
| Insider misuse of credentials | Privileged access abuse | IP theft, customer data leakage |
Cybersecurity Consulting. From Cyber Risk to Strategic Investment
We help clients focus resources on reducing the most consequential risks, not just the most visible threats.
Risk & Exposure Mapping
Identify critical assets, threat vectors, and likely attack paths
Business Impact Correlation
Map cyber risks to operational, financial, and regulatory outcomes
Acceptable Risk Definition
Define what level of risk the business can tolerate
Capability Gap Identification
Detect overinvested areas and vulnerable weak points
Risk-Aligned
Roadmap
Prioritize capabilities that reduce risk where it matters most
Smart Reallocation & Execution
Optimize resources for max impact; measure with KPIs
Scenario-Based Cyber Risk Modeling for Informed Decision-Making
Our cybersecurity consulting services are rooted in advanced risk modeling tools and methodologies. These help our clients analyze real-world cyber scenarios and make evidence-based decisions. By modeling potential threats stakeholders cand take measurable, business-aligned risk decisions.
| Business Scenario | What We Analyze | Value Delivered |
| Ransomware attack on operations | Downtime cost, recovery time, exposure points | Focused investments in backup and recovery where impact is high |
| Customer data breach | Breach likelihood vs. financial/regulatory impact | Informed decision to deploy DLP and increase monitoring |
| Critical vendor outage | Supplier dependency and risk concentration | Identified high-risk vendors and enforced stronger controls |
| Former employee retains access to systems | Insider threat paths, access risk | Closed security gaps, reduced risk of internal sabotage |
| Delayed IT infrastructure upgrade | System failure probability, business cost of downtime | Built clear ROI case for prioritizing upgrade investment |
Prepare Your Organization Before an Incident Happens
What could you benefit from when choosing our cybersecurity consulting services:
While many organizations have an incident response policy on paper, few have tested it. We go beyond theory with hands-on planning and simulation exercises to increase vigilance and readiness across your teams.
- Customized Incident Response (IR) Playbooks tailored to your environment
- Tabletop Exercises simulating real-world attack scenarios for leadership and technical teams
- Cross-functional drills involving IT, legal, compliance, and communications
- Gap analysis and actionable after-action reports
- Integration with business continuity and disaster recovery processes
We help you turn your incident response plan into a repeatable, effective process—ready for the real world.
Preparing for the Future: vCISO advancements
Executive-Level Security Insight: A Growing Enterprise Demand
Virtual CISO (vCISO) models are gaining momentum, with the global market projected to reach $3.8 Billion by 2033, growing at a 12.2%+ CAGR. This surge reflects a rising demand for a stronger executive-level cybersecurity oversight. As part of our cybersecurity consulting work, we remain closely aligned with the organizations’ needs, supporting informed decisions that reflect evolving expectations around leadership, compliance, and strategy.
Strategic Reporting for Boards and Executives
In 2025, 92% of CEOs express confidence in their cybersecurity strategy yet only 5% of security leaders fully agree. This reveals a major disconnect between executive perception and operational reality. The gap can be filled either by vCISOs, or by a tailor-made strategy that includes assigning responsibilities and roles. Within our cybersecurity consulting engagements, we emphasize reporting that transforms technical detail into business-relevant insight. Our approach supports leadership teams in communicating cyber risk clearly, concisely, and effectively at the board level.
Integrated Security Programs with Strategic Alignment
While virtual CISO services address the need for executive security leadership, many organizations benefit greatly from focused cybersecurity consulting that helps build and optimize comprehensive security programs. Our expertise supports businesses in aligning risk management, compliance, incident response, and vendor oversight with their unique operational goals. This approach ensures security initiatives are cohesive, prioritized, and deliver measurable business value.
The Latest Statistics on Cybersecurity Paint a Somber Picture
A recent study highlighted that companies around the globe spend an average of $164,400 (12.9% of their total IT Security Budget) on manual penetration testing assessments. As 60% of organizations choose to implement pen testing at least twice a year, it is important to have a strong partnership with a team of experts to ensure availability to periodical assessments. Our cybersecurity specialists have extensive expertise in offering penetration testing services for various industries, helping enterprises strengthen their protection & be prepared for potential threats.
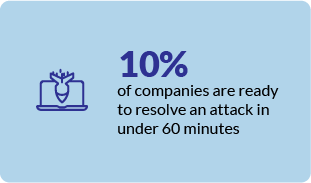
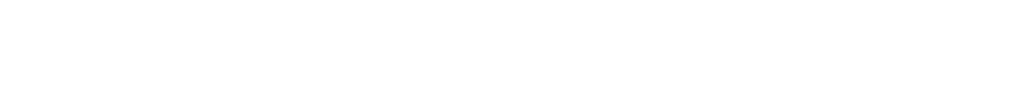
According to IBM’s data breach report, in 2023, the average cost of a data breach was $4.45 mil. There has been a 15% increase in the last three years, which seems to motivate organizations to focus more on security investments and, indeed, on partnerships with experienced cybersecurity service providers. 51% of them plan to increase protection through various measures (incident response, planning and testing, training for employees, threat detection, tools of response).
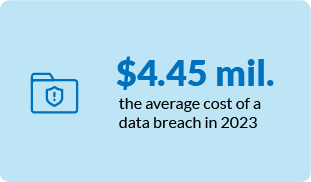
The continuously growing cyber threats highlight that companies must enforce security measures immediately. According to the EC-Council CEH Threat Report 2024, 62% of companies respond to incidents in more than 2 hours, and only 10% are ready to resolve an attack in under 60 minutes. Regular training and cyber drills (simulated attacks on systems), real-time monitoring, and having an incident response plan and team are essential to avoid financial loss, data leakage, and reputational damage.
Cybersecurity starts with Secured Software Development
Given the increased frequency of cyber threats, we adopt a proactive stance in our activity, fostering a culture of heightened security awareness among our team. Continuous improvement is at our core, with workshops focusing on the latest security standards, including ISO 27001:2022, focusing on secure coding controls. Our commitment extends to certain software development practices and tools, ensuring the resilience of your information systems.
Secure your business with us!
What Are the Steps in Cybersecurity Implementation?
START
Discover your organization’s
current security posture and
vulnerabilities through an
automated assessment.
FIX

Implement robust security
measures in your organization
to avoid data leaks, financial
loss, fines and reputational
damage.
TRAIN

Ensure the internal team’s
awareness of the most
recent digital threats and
best practices to protect
from cyberattacks.
REPEAT
Conduct periodical security
assessments and continuously
enhance safety measures in
your organization to avoid
new cyber threats.

How to Protect Your Organization? Discover the AROBS Managed Security Services
Security Assessment
Ensure your company's protection through regular scans to identify vulnerabilities, followed by efficient management and remediation of identified risks.
Work with us
Expose weaknesses in applications, systems or network services through authorized simulated cyberattacks that demonstrate potential methods used by an entity to exploit weaknesses.
Work with us
Security Operations
Compliance and Incident Response
Looking for Enterprise Cybersecurity Solutions?
Meet our Experts

Claudiu Mailat
Delivery Director, Travel, E-commerce & Cybersecurity
Claudiu has a strong expertise in driving business development across sectors, including Travel, AI, Cybersecurity, E-commerce, and SAP. With a proven record of leading strategic projects, building long‑term client relationships, and executing innovative growth initiatives, Claudiu leverages technology to deliver scalable solutions and operational efficiency. He oversees business development and project delivery, guiding cross‑functional teams, accelerating market expansion, and ensuring high‑quality, customer‑focused software solutions.

Romeo Andreica
Chief Information Security Officer & Security Auditor by DNSC
Romeo has strong expertise in cybersecurity, IT, networks, and telecommunications, backed by Cybersecurity PhD research, providing a powerful foundation for security and compliance. As CISO, Romeo implements measures, policies, and procedures in line with security standards and European legislative requirements (e.g., ISO 27001, TISAX, GDPR, NIS, ISO 42001). As a certified CISM, CEH, and ISO 27001 auditor, Romeo strengthens organizational resilience through continuous monitoring, vulnerability management, and company‑wide security awareness initiatives.
What Are the Reasons Why Cybersecurity Is Important Now More Than Ever?
The probability of cyberattacks has severely increased. A Cybersecurity Ventures Report shows that global ransomware could
reach 42 billion dollars by 2024 and even exceed 265 billion by 2031.
Cybersecurity services are not just about risk management. They’ve become an essential part of the strategic development
process, merged in every aspect of its layers: from staff training and awareness to product creation and end-consumer.
Data Protection
One of the most valuable assets is your company's confidential data. Securing access is vital for the organization, employees, and business partners.
Financial Security
It protects your intellectual
property and corporate
information to avoid activity
disruption and potential money
loss.
Reputation
Helps maintain a trustworthy and clean reputation in the industry, protects clients' and customers' trust, avoids a media crisis, and wins over new clients.
Productivity & Secure Operations
A secure system assures an
uninterrupted productivity cycle,
leading to meeting standards and
delivery deadlines.
Product Quality
Creating products with
integrated security layers makes
them a top-shelf option for
buyers.
Customer trust
Consumers are aware of the digital
threats and are looking for
security-focused products and services.
Positioning your business as a standard
compliant company differentiates you
from competitors.
Secure your business with us!
Our Cybersecurity Expertise
With over 50 accredited certifications, our team specializes in penetration testing, process audits, vulnerability management, preventive actions, and threat hunting. Together with our cybersecurity experts, we can protect your company against threats, setting new standards for information security in your company. Also, our Security and Compliance department, including our experts, contributes to conducting, developing, monitoring, and auditing all implemented technical and organizational measures related to the secure development process according to the industry, customer, legislative, and business requirement.
Given the context, investing in enterprise cybersecurity solutions and information security is a top priority today for organizational health; it can assure your company’s resilience under unpredictable circumstances. The AROBS team is well prepared to create and maintain your organization safe through various methods and techniques such as penetration testing services, to identity and access management, incident response and forensics, trainings and more. Discover below our suite of cybersecurity services.
What Are the Top Emerging Trends in Cybersecurity?
Digitalization increases, and so is the frequency of cyberattacks. In this context, Europe and US’s top industries are the main targets of cyberattacks – finance, healthcare, and retail. Moreover, the intense use of cloud computing and the Internet of Things (IoT) is a gate for new vulnerabilities. So, it is crucial to work closely with a cybersecurity services provider who can find the proper solutions adapted to custom business needs.
Garnter specialists identified 6 trends that are shaping cybersecurity measures in 2024, encouraging a proactive approach in taking security measures, identifying threats and training employees to recognize and avoid cyber threats.
- Generative AI – large language model (LLM) applications are the beginning of disruption and specialists recommend using GenAI tools in a safe and ethical way.
- Outcome-driven metrics – adopting such metrics helps business stakeholders keep track of the benefits brought by investments in advanced protection.
- Reducing human-related cybersecurity risks – there is an increased focus on employee awareness by introducing security behavior and culture programs (SBCP).
- Third-party risk management – organizations should pay more attention to external partners and create security protocols to protect their mutual data and assets.
- Continuous threat exposure management (CTEM) – creating a system to expose assets to vulnerabilities through various techniques, including pen testing, can reduce breaches by up to two-thirds by 2026, according to Gartner.
- An identity-first approach – Identity & Access Management (IAM) must be upgraded with the latest practices to avoid unauthorized access to any organization’s system and data.
Cybersecurity for industries
Public institutions
Among the most threatened organizations are public institutions that own an immense amount of confidential data that can affect general security and safety. Thus, our company collaborates with the public institutions in our present communities by being involved in the digitalization process and providing secure solutions.
Banks and financial institutions
Fintech is growing expertise in our company's portfolio. Developing financial technology solutions involves including information security operations from scratch, which we strive to accomplish in our projects.
Healthcare institutions
Our healthcare software division provides solutions at the highest quality and security standards for significant stakeholders in the e-pharma industry and clinical trials. Health records, clinical research, patients records, and social security numbers are all protected by the software's complex architecture that we build.
Travel
The travel industry is also an area of expertise for AROBS. The hotel industry attracts cyberattacks due to many financial transactions online during the booking process. Working with large reservation platforms serving thousands of clients has helped us design and implement robust information security systems that successfully prevented cyberattacks.
Corporations
Visible businesses such as large corporations are equally vulnerable as they are exposed. Public business data can lure potential cybersecurity attacks very easily. Being ourselves in this category, we know very well that valuable information such as product concepts, intellectual property, strategies, client databases, and contracts must be protected by various layers of information security. To ensure your organization can surpass a cyberattack successfully, we support these security layers with penetration testing services.
// Arobs Transilvania Software
Latest case studies
Our clients share the experiences they had working with us. AROBS case studies explain our most provocative projects.
// our recent news
Read Our Latest News

Blog
AROBS completes the merger by absorption process to simplify the Group structure and increase operational efficiency
Read More »
camelia.oltean
April 9, 2026

Blog
AI-Ready Cockpit Domain Controller: the Automotive AI Assistant Built for Context-Aware Mobility
Read More »
Diana-Maria Coste
April 1, 2026