AROBS Transilvania – custom software development company
AROBS Transilvania Software development > Blog > Stealth in Cyberspace: The Secrets of Steganography in Information Security
Stealth in Cyberspace: The Secrets of Steganography in Information Security
The realm of software development and enterprise cybersecurity solutions is complex. At their intersection, the art of concealing sensitive information, steganography, can be viewed from two distinct perspectives. On the one hand, hiding data in plain sight can safeguard against potential threats to confidential information. However, this technique also poses a risk, as malicious actors could use it to exploit valuable data.
In this enlightening article penned by our colleague, Romeo A., Chief Information Security Officer, we delve into the fascinating world of steganography techniques. Discover how an ancient practice has become an asset in protecting sensitive data in different file types.
Introduction
In the ever-evolving world of information security, techniques for hiding data are constantly advancing. Steganography, the art of concealing information within seemingly innocuous files, plays a significant role in safeguarding sensitive data. Steganography, an ancient practice dating back to ancient Greece, has found its place in the digital age as a powerful technique for hiding secret information within various file types. This article explores the concept of steganography and its relevance to cybersecurity, including its use in cyber attacks, malware, and noteworthy examples.
Understanding Steganography
Steganography is the practice of hiding information within other non-secret files, making it invisible to the naked eye. Unlike cryptography, which focuses on encrypting data, steganography aims to ensure that the very existence of the hidden information goes unnoticed. This technique employs various digital mediums, including images, audio files, video files, and even text documents, to embed secret data. By utilizing subtle changes in these files, steganography ensures that the hidden information remains concealed from prying eyes, using lot of hiding algorithms:
- Least Significant Bit (LSB) Substitution: LSB substitution is a simple and widely employed algorithm. It replaces the least significant bits of the carrier file’s pixels or bytes with the secret data. Since altering the LSB has minimal impact on the visual or auditory quality of the file, the hidden information remains concealed.
- Spread Spectrum: The spread spectrum algorithm distributes the secret data across multiple frequencies or locations within the carrier file. By spreading the data, it becomes harder to detect and extract without the knowledge of the specific spreading technique used.
- Transform Domain Techniques: Transform domain techniques, such as Discrete Cosine Transform (DCT) or Discrete Wavelet Transform (DWT), exploit mathematical transformations to hide secret data within the frequency domain of the carrier file. These techniques provide robustness and resistance against steganalysis.

Different file types require specialized steganographic techniques for effective concealment. Here are a few examples:
- Image Steganography: Image steganography techniques exploit the characteristics of image formats like BMP, JPEG, or PNG. These techniques alter pixel values, color channels, or frequency components to embed secret data while ensuring the visual quality of the image remains intact.
- Audio Steganography: Audio steganography techniques focus on embedding secret data within audio files, such as WAV or MP3. They manipulate audio samples or utilize frequency domain transformations to hide the information seamlessly within the sound signal.
- Document Steganography: Document steganography techniques involve concealing secret data within textual documents like PDF or DOCX. These techniques leverage elements like whitespace, font style, or specific characters to encode the hidden information discreetly.
3. Steganography Tools
Modern steganography relies on a range of specialized tools and software applications designed to embed secret information within files. These tools offer various features and functionalities, making the process of concealing data more efficient and effective. Some popular steganography tools include:
- OpenStego: OpenStego is an open-source steganography software that supports multiple carrier file formats, including images and audio files. It utilizes techniques like LSB replacement and matrix encoding to embed secret data and provides encryption options for added security.
- Steghide: Steghide is another widely used command-line tool that allows users to embed secret information within various file types, such as images, audio files, and documents. It supports encryption and passphrase protection for the hidden data.
- OutGuess: OutGuess is a popular steganography tool capable of hiding information within JPEG images. It employs a sophisticated algorithm that takes advantage of the image’s least significant bits (LSBs) to embed the secret data.
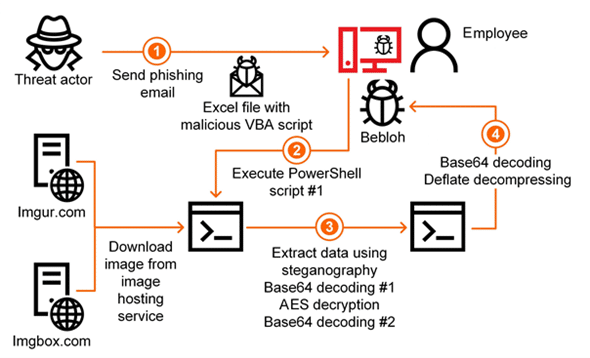
4. Steganography in Cyber Attacks
Cyber attackers frequently employ steganography to carry out their malicious activities. They embed malicious code within innocent-looking files, which can then be distributed across networks or shared online. Once the unsuspecting user opens the seemingly harmless file, the hidden payload is unleashed, compromising the victim’s system or network. The use of steganography in cyber attacks allows hackers to bypass traditional security measures and increase their chances of successful infiltration. By disguising malware within legitimate files, attackers exploit the trust placed in common file types, making detection and prevention more challenging.
One popular steganographic technique in cyber attacks involves embedding code within image files, such as PNG (Portable Network Graphics). PNG files use lossless compression, allowing the embedding of additional data without visibly affecting the image quality. Attackers can use algorithms like the Least Significant Bit (LSB) technique, which replaces the least significant bits of the image’s pixel values with the hidden information. This alteration is often imperceptible to human observers. A steganographic attack is the art and science of embedding hidden message or malware in a carrier medium such as an image or video file in a way of the recipient does not realize the file is malicious.

To detect alterations in PNG files, integrity checks can be performed using checksums or cryptographic hashing algorithms such as MD5 or SHA-256. These algorithms generate unique hashes for files, acting as a digital fingerprint. By comparing the computed hash of an original file with the hash of a potentially altered file, discrepancies can be identified, indicating possible tampering.
5. Steganography and Malware
Malware authors also utilize steganography to enhance their malicious payloads. Rather than using plain text or easily identifiable code, steganography allows them to embed malware within images, audio files, or even seemingly harmless documents. By hiding the malicious code within these files, malware authors can bypass security scanners that typically focus on known malware signatures. As a result, steganography becomes an effective technique for evading detection, enabling the stealthy distribution of malware. Once the infected file is executed, the hidden malware is unleashed, compromising the victim’s system and potentially providing attackers with unauthorized access to sensitive data.
6. Detecting Steganographic Exploits
Detecting steganographic exploits poses a significant challenge for cybersecurity professionals. Traditional signature-based detection mechanisms often fail to identify hidden exploit code, as the signatures typically focus on known malware patterns rather than steganographic techniques. However, advanced threat detection approaches can aid in identifying such threats. These may include:
- Behavioral Analysis: By monitoring the behavior of files or processes, security solutions can identify suspicious activities associated with steganographic exploits. Unusual file interactions, unexpected network connections, or abnormal system behavior may indicate the presence of a hidden exploit.
- Machine Learning Algorithms: Leveraging machine learning techniques, security systems can be trained to recognize patterns and anomalies associated with steganographic exploits. By analyzing file structures, pixel values, or audio properties, machine learning models can identify hidden content that deviates from normal patterns.
- Heuristic Scanning: Implementing heuristics-based scanning techniques enables security systems to detect unknown or previously unseen steganographic exploits. These techniques involve analyzing file characteristics, such as file size, entropy, or irregularities, to identify potential instances of hidden code.
7. Conclusion
Steganography continues to be a powerful tool for attackers seeking to conceal their intentions and payloads. As technology advances, so does the sophistication of steganographic techniques. To effectively counteract the risks associated with steganography, organizations must implement robust security measures that include advanced threat detection systems capable of identifying hidden data within seemingly innocuous files. Steganography, with its array of tools and algorithms, provides a covert means of hiding secret information within various file types. As technology advances, the field of steganography continues to evolve, demanding robust countermeasures to detect and prevent its misuse. Understanding the technical intricacies of steganography empowers information security professionals to develop effective defense strategies against potential attacks.
References
https://www.giac.org/paper/gsec/1714/steganography-past-present-future/101649
https://www.sciencedirect.com/topics/computer-science/steganographic-technique
https://link.springer.com/article/10.1007/s11042-023-15568-7
https://www.hindawi.com/journals/scn/2017/5397082/
https://builtin.com/cybersecurity/steganography
https://www.malwarebytes.com/blog/news/2022/08/explained-steganography
https://blog.sucuri.net/2023/05/what-is-steganography-how-hackers-hide-malware-on-websites.html
// Let us be the partner that helps your business adapt to change.
Leave us a message for a digital upgrade!
// our recent news
Read our recent blog posts
Blog
AROBS reports consolidated revenue of RON 144 million in Q1 2026 and a 12% increase in net profit
Read More »
Diana-Maria Coste
May 19, 2026



