AROBS Transilvania – custom software development company
AROBS Transilvania Software development > Blog > The Impact of Artificial Intelligence and Machine Learning on Cybersecurity
The Impact of Artificial Intelligence and Machine Learning on Cybersecurity
As Artificial Intelligence and Machine Learning continue their evolutionary journey, they remain indispensable assets in navigating the ever-evolving landscape of cyber threats. This transformative technology equips software development processes with innovative means to shield their digital ecosystems against emerging adversities. Our highly experienced colleague, Romeo A., Chief Information Security Officer, helps us discover how AI/ML can be used both as a defensive and offensive solution in organizations.
Continue reading to learn about the double facets of Artificial Intelligence and Machine Learning, empowerment, and vulnerability, and how they interfere with cybersecurity.
In recent years, Artificial Intelligence and Machine Learning have emerged as game-changers in the realm of cybersecurity. Its unprecedented ability to analyze vast amounts of data, identify patterns, and adapt in real-time has revolutionized the way organizations defend against cyber threats. This article delves into the profound impact of AI on cybersecurity, highlighting its pivotal role in safeguarding sensitive data, detecting emerging threats, and fortifying the digital landscape against evolving cyberattacks.
A Brief Context on Artificial Intelligence
AI has advanced rapidly, leading to a multitude of innovations and advantages. Nevertheless, it has also created opportunities for malevolent actors to exploit these breakthroughs. So, what has been AI’s impact on cybersecurity thus far? How are cybercriminals leveraging new tools, and how are companies addressing these challenges?
A prime illustration of the current state is ChatGPT, a potent AI language model crafted by OpenAI. As AI technology becomes more accessible, comprehending its influence on cybersecurity becomes indispensable. We will explore both the positive and negative implications of AI on security while delving into viable solutions to safeguard our digital realm.
The Evolution of Cyberattacks: From Simple Malware to Complex Ransomware Assaults
Over the years, cyberattacks have undergone a dramatic transformation, progressing from rudimentary malware like Bob Thomas’ Creeper in the 1970s to highly sophisticated assaults targeting multiple facets of an organization’s infrastructure. Notably, ransomware attacks have emerged as a prominent example of this evolution.
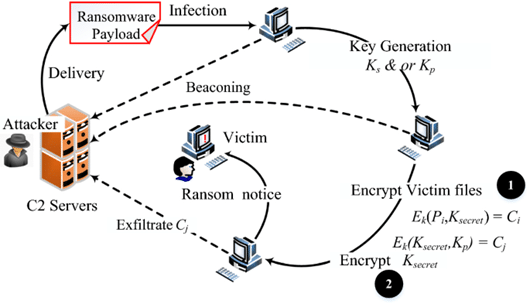
In 2017, the infamous WannaCry ransomware attack shook the world, impacting not only the NHS but organizations globally. The attack encrypted valuable data and demanded a ransom for its release. Since then, ransomware attacks have evolved, adopting even more cunning techniques such as double and triple extortion methods. In the double extortion approach, hackers not only encrypt the victim’s data but also exfiltrate sensitive information, holding it hostage to demand payment for both the decryption key and assurance that the stolen data won’t be exposed. The triple extortion strategy takes it a step further, targeting both the organization and individuals affected by the data breach, coercing additional payments.
To counter these advanced threats, organizations have implemented vulnerability management programs. These programs focus on identifying, tracking, and promptly remediating infrastructure vulnerabilities to minimize the risk of exploitation. Security teams have also embraced proactive threat-hunting techniques, leveraging tools like Endpoint Detection and Response (EDR) and Security Information and Event Management (SIEM) platforms. This enables them to actively seek out suspicious network activities and respond swiftly to potential threats. While these measures prove effective against known vulnerabilities, they may fall short when it comes to undisclosed zero-day vulnerabilities, underscoring the need for continuous vigilance and innovation in the field of cybersecurity. To safeguard against the ever-evolving threat landscape, organizations must remain agile, adaptive, and committed to staying one step ahead of cybercriminals. This can be resolved using AI.
AI’s Dual Impact in Cybersecurity: Malware Development and Vulnerability Detection
The rise of AI in the realm of cybersecurity has brought about a complex interplay of offensive and defensive applications. Cybercriminals are harnessing AI’s power to create highly sophisticated malware that can adeptly evade traditional security systems. This intelligent malware autonomously spreads through networks, identifies high-value targets, and dynamically adjusts its attack tactics to overcome existing defenses.
On the other side of the spectrum, AI serves as a potent ally for cybersecurity professionals seeking to fortify their digital fortresses. Using AI-driven solutions, security experts can analyze vast amounts of code, swiftly identifying potential weaknesses and zero-day vulnerabilities in software applications. This proactive approach empowers organizations to address vulnerabilities before malicious actors can exploit them, thereby significantly strengthening their overall security stance.
In essence, AI’s dual role in cybersecurity highlights its profound impact on both the escalation of cyber threats and the fortification of defense mechanisms.
Here are some examples of how AI can fortify defense mechanisms in cybersecurity:
- AI-powered threat detection: AI algorithms can analyze vast amounts of data in real-time, enabling the identification of anomalous behavior and potential cyber threats with higher accuracy and speed.
- Behavioral analysis: AI can track and analyze user behavior patterns to detect deviations from normal activity, flagging potential insider threats or unauthorized access attempts.
- Automated incident response: AI-driven systems can autonomously detect and contain threats, initiating immediate response actions to mitigate the impact of cyber incidents.
- Network traffic analysis: AI can continuously monitor network traffic to detect unusual patterns, identifying potential intrusion attempts and facilitating quick response measures.
- Predictive analytics: AI algorithms can predict emerging cyber threats based on historical data, enabling proactive defense measures before attacks occur.
- Vulnerability management: AI can automate vulnerability scanning, prioritizing critical weaknesses for timely patching and reducing the window of opportunity for attackers.
- Malware detection and analysis: AI-powered solutions can identify and analyze new and unknown malware variants, enhancing the ability to counter evolving threats.
- User authentication and access control: AI can improve authentication systems by incorporating multi-factor authentication and adaptive access control based on user behavior analysis.
- Threat intelligence analysis: AI can process and analyze vast amounts of threat intelligence data from various sources to identify potential threats and vulnerabilities in real-time.
- Security automation and orchestration: AI-driven automation streamlines security processes, freeing up human resources for more strategic tasks and improving response times.
As cyber adversaries increasingly utilize AI as a weapon, organizations must adopt AI-driven tools and strategies to maintain a proactive stance against these evolving threats. By leveraging AI’s capabilities, cybersecurity can become more resilient, staying one step ahead in the ongoing battle to secure the digital landscape.
Utilizing AI for Internal Testing and Vulnerability Assessments
The escalating prominence of AI in the cybersecurity domain has facilitated its integration into the realm of internal testing and vulnerability assessment protocols. Through the implementation of AI-driven methodologies, security teams can conduct penetration testing, vulnerability scans, and code analysis with heightened efficiency and efficacy compared to conventional approaches.
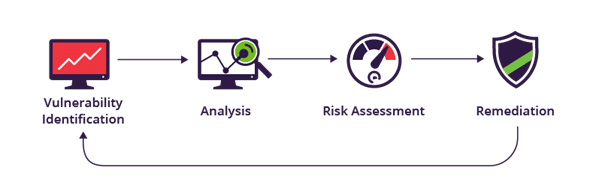
These AI-driven tools facilitate the automatic identification of security vulnerabilities, extensive analysis of data sets, and adept adaptation to emerging threat vectors. By proactively pinpointing and remedying potential security loopholes, organizations can thwart cybercriminals’ attempts to exploit these weaknesses. This proactive stance not only reinforces an organization’s comprehensive security posture but also significantly curtails the susceptibility to successful cyberattacks. As a result, AI is emerging as an indispensable asset for organizations committed to maintaining heightened vigilance amidst the perpetually shifting terrain of the cybersecurity landscape.
Ensuring Machine Learning Security
Machine learning (ML) algorithms, once liberated from the controlled environment of the laboratory and introduced into the real world, can become susceptible to various forms of attacks crafted to manipulate ML systems into making intentional errors. Adversaries might taint training datasets or decipher the model’s code. Moreover, hackers can engage in ‘brute-forcing’ of ML models using specialized ‘adversarial AI’ to automatically generate numerous attacking samples until they expose a vulnerability in the model. The repercussions of such attacks on ML-based anti-malware systems could prove catastrophic, misidentifying Trojans potentially leading to device infections on a massive scale and substantial financial losses.
Considering this, several vital considerations must underpin the utilization of ML within security systems:
- Security vendors must comprehend and address fundamental performance requirements of ML within the actual, potentially antagonistic, operational environment. This entails ensuring robustness against potential adversaries. Incorporating ML/AI-specific security audits and ‘red-teaming’ exercises should constitute integral aspects of Artificial Intelligence and Machine Learning development.
- When evaluating the security of an ML solution, scrutiny is essential regarding the extent to which the solution relies on third-party data and architectures. Numerous attacks are predicated on third-party inputs, encompassing threat intelligence feeds, public datasets, pre-trained models, and outsourced ML models.
- ML methodologies should not be perceived as a remedy. They should function as components of a multi-layered security approach where a blend of complementary protection technologies and human expertise collaborates, forming a cohesive line of defense.
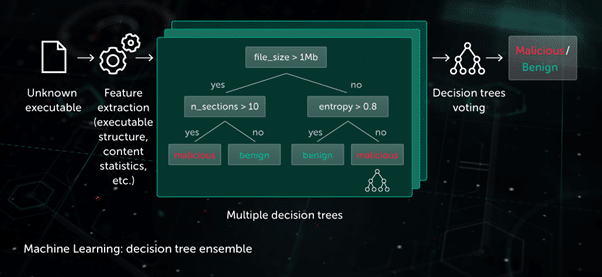
For example, the context of the “decision tree” approach, the predictive model takes on the structure of a collection of decision trees (e.g. random forest or gradient boosted trees). Each non-leaf node within a tree poses a question regarding specific file features, while the leaf nodes hold the tree’s ultimate verdict on an object. During the testing phase, the model navigates through the tree by responding to the queries in the nodes using the relevant features of the considered object. Ultimately, the conclusions from multiple trees are amalgamated in a manner dictated by the algorithm, yielding the ultimate decision on the object.
This model proves advantageous in the Pre-Execution Proactive protection stage on the endpoint side. One application of this technology lies in Cloud ML for Android, employed for mobile threat detection.
Outlines on using Artificial Intelligence and Machine Learning in Cybersecurity
We’ve explored the transformative impact of Artificial Intelligence and Machine Learning on cybersecurity, witnessing its dual role in both enabling advanced threats and fortifying defense mechanisms. AI’s proficiency in threat detection, adaptive phishing campaigns, and automating vulnerability assessments showcases its potential for malicious exploitation. Simultaneously, AI/ML empowers cybersecurity professionals to detect anomalies, predict vulnerabilities, and orchestrate incident responses with unprecedented speed and accuracy. As AI/ML continues to evolve, it remains an indispensable tool in navigating the dynamic and ever-evolving landscape of cyber threats, enabling organizations to proactively safeguard their digital ecosystems against emerging adversities.
References
https://identitymanagementinstitute.org/using-artificial-intelligence-in-cybersecurity/
https://www.analyticsvidhya.com/blog/2023/02/future-of-ai-and-machine-learning-in-cybersecurity/
https://www.balbix.com/insights/artificial-intelligence-in-cybersecurity/
https://cyberstartupobservatory.com/artificial-intelligence-cyber-security/
https://www.xenonstack.com/blog/machine-learning-cybersecurity
// Let us be the partner that helps your business adapt to change.
Leave us a message for a digital upgrade!
// our recent news
Read our recent blog posts

Blog
AROBS completes the merger by absorption process to simplify the Group structure and increase operational efficiency
Read More »
camelia.oltean
April 9, 2026



